Phishing for Info
by Taylor Derrisaw | published Apr. 10th, 2016
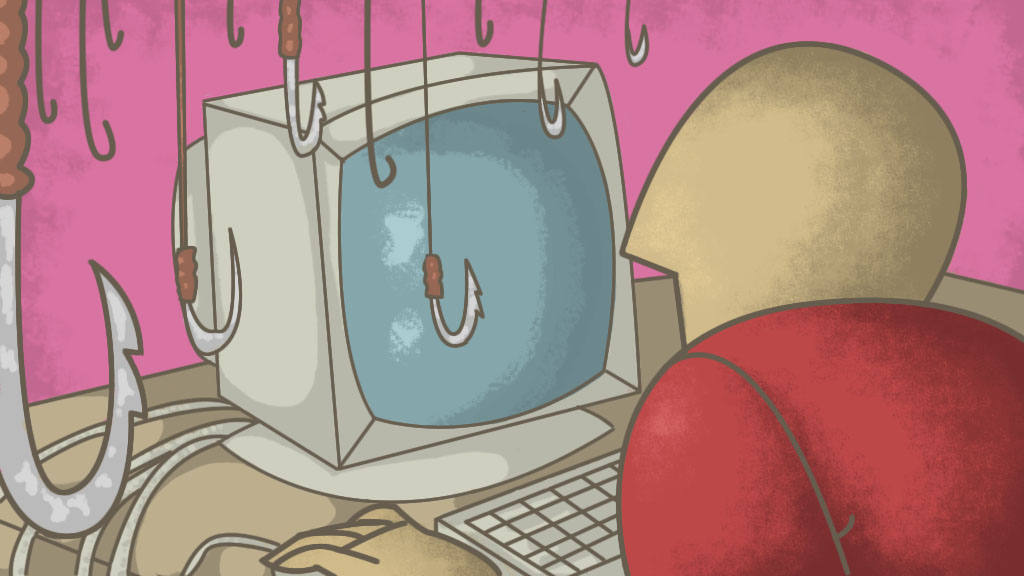
An unknown hacker has been attempting to retrieve information from RIT's email networks. This is a dangerous practice known as phishing.
Phishing is the act of posing as a legitimate company or individual to gain information by misleading or compromising an online account. This is a popular method, as getting the target to release information is usually easier than breaking into whatever kind of information the hacker is searching for.
Recently, RIT was attacked by an unknown hacker who was attempting to illegally retrieve information from RIT’s email network. RIT’s Information Security Office (ISO) noticed the breach in mid to late March, and attempted to halt the scheme. In the weeks that followed, the ISO noticed that many accounts were being compromised by the phishing scam. So far, they have identified approximately 60 compromised accounts. Ben Woelk, ISO Program Manager, is one of the administrators looking into the attack.
“There would be one that comes in and targets 15 people," Woelk said. "Things were not coming through the mail gateway in a high enough volume that you could do anything to filter them out."
The phishing scam utilized files that enticed the recipient to click on them. The file might have been labeled as a word document but could’ve opened as a completely different file type.
So far, the ISO believes that the hacker resides in China or Russia, but cannot confirm that at this time. Woelk believes universities are consistently targeted for the research data they have.
One of the main challenges in combating phishing is the complexity of the hackers’ abilities. In the past, phishing scams were easily distinguishable by things like spelling errors, but now hackers can purchase phishing templates online. Not only does this lead to variety of phishing “styles,” but it also makes the attempts harder to spot.
Despite the efforts of the administration, it is nearly impossible to determine exactly when and how these cyberattacks will manifest. Therefore, students and faculty must be vigilant and watch out for anything that seems out of the ordinary or malicious.
“The problem with information security is that we are reactive, not proactive, because it’s hard to determine what the adversaries are going to do next," Woelk explained. "If we spend too much energy on one thing, they might attack in another direction."
Students can avoid the phishing scams by looking for things that seem out of the ordinary. If you didn’t expect to receive something, don’t open it. If a friend sends a link to something over email, verify it with them to ensure it’s not malicious. Oftentimes hackers will attempt to create a sense of urgency within the recipient. Threats that tell the recipient their account will be deactivated if they do not renew their password is a common strategy, and RIT has gone through this scenario before. Often times, these emails will be written in a very generic tone, according to a pamphlet provided by the ISO. This tone is often an indicator of a phishing attempt.
Currently, RIT has a spam filter that students and faculty can modulate to their preference. Woelk warns, however, that too many filters could prevent important emails from coming through. It really comes down to balancing out and being vigilant about what kinds of information you want to screen for. Woelk advocates caution, and that individuals shouldn’t assume that they’re invulnerable from phishing attempts.
If any RIT student or faculty member suspects a phishing attempt, they are encouraged to contact spam@rit.edu. If they have any questions they are encouraged to contact infosec@rit.edu.
More information can be obtained from the ISO’s website at http://rit.edu/security.